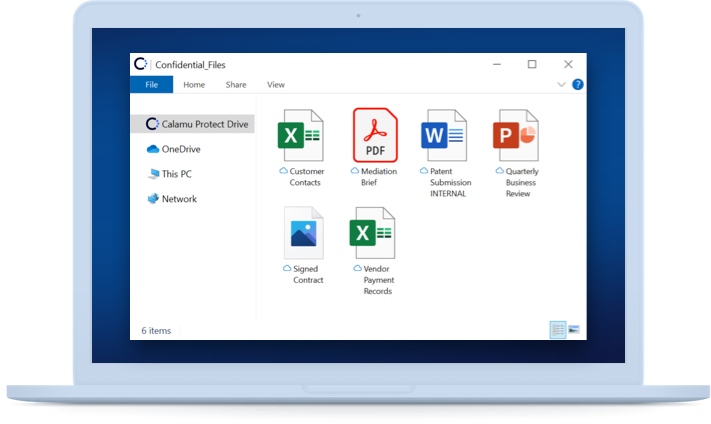
Calamu Protect™
The Data-First Security Platform
Add unprecedented cyber resilience to stored data, anywhere.
Learn more about the components of Calamu Protect
The Safe Data Harbor
Calamu Protect™ fragments data across multiple separate storage locations, an environment called a data harbor, instantly nullifying the impact of a data breach or ransomware attack and adding near infinite resilience.
Learn More About Data Harbors From Inc Magazine
Secure
Protects against data theft and extortion. Calamu'd data is worthless to cyber attackers.
Resilient
Automatically self-heals from cyber attacks. Data remains available as if nothing happened.
![]()
Compliant
Meets data privacy regulations. Using Calamu Protect enables compliance with international laws and standards.